The AnomaPay Public Beta is Live on BNB Chain
The easiest way to pay privately onchain is now live on BNB Chain and open to everyone.

The easiest way to pay privately onchain is now live on BNB Chain and open to everyone.








Check your eligibility and register now for season 1 of the Anoma XAN airdrop.



















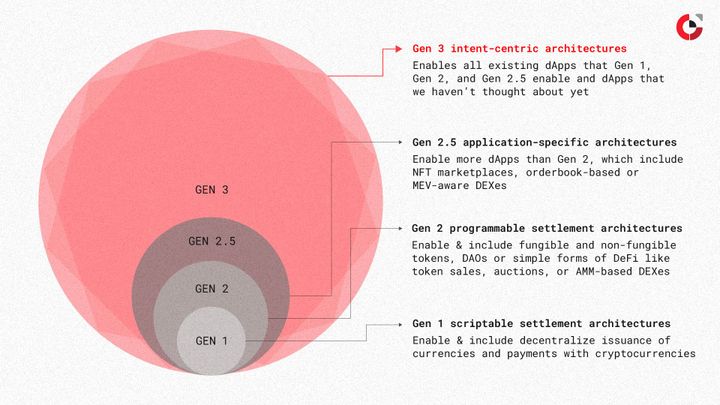
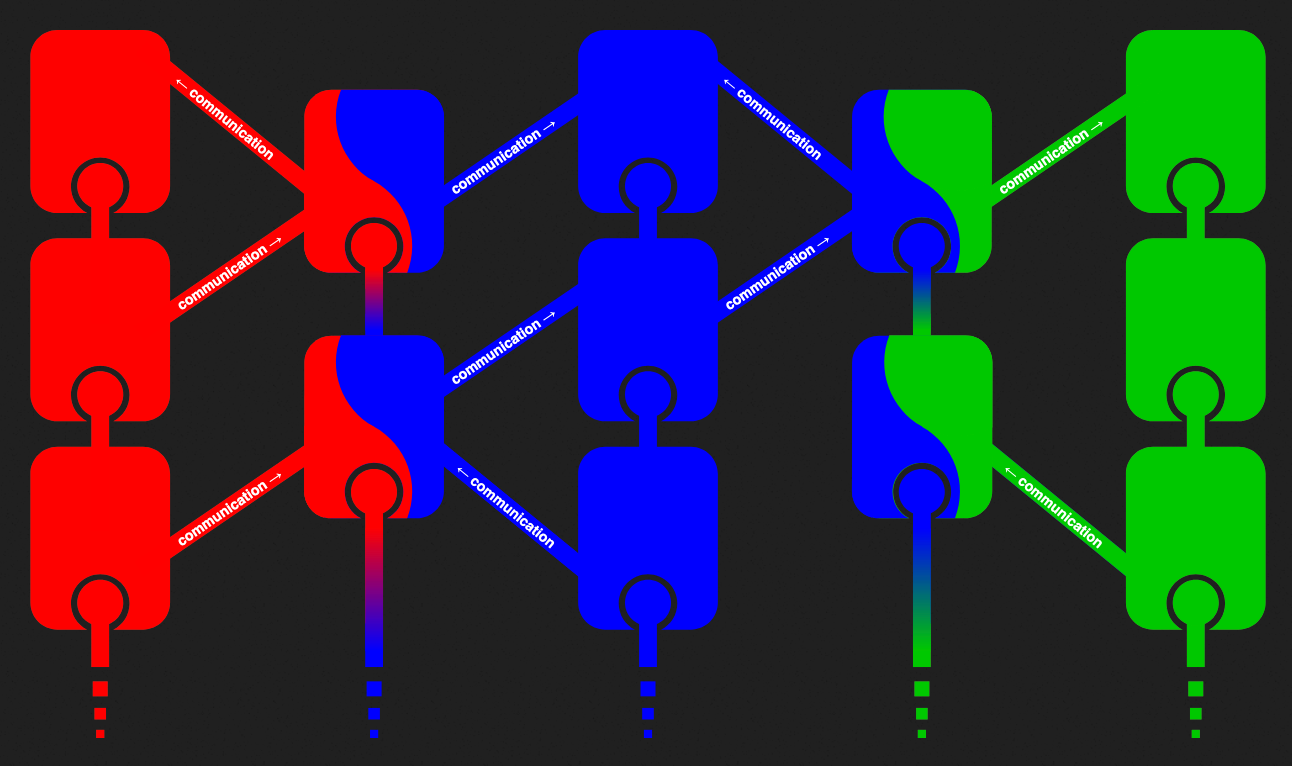
In our follow-up to intent-based protocols pt.1 we examine SUAVE - a marketplace for MEV mechanisms.


In part 1 of our series on intent-based protocols, we break down UniswapX.